Sharing data is easy. Protecting it is not.
Unclear Access Rights
Opaque Data Flows

No Defensible Evidence
on:mint provides it
Connected Data Spaces
Case Study: From simple sharing to precise access control
01
Control data flows
02
EU-compliant storage

03
Track usage & enforce rights
04
Legally binding approvals & execution
• Use Cases
How on:mint protects your sensitive data streams
Pharma: Certification with multiple partners
Research: Collaborative projects with partner institutions
Media & Creative Industries: Secure release of raw material
• Before / After
Control instead of loss of control
• SECURE IT NOW
Collaborate securely on confidential projects
FAQs
What are Connected Data Spaces and which problem do they solve?
Connected Data Spaces are secure, collaborative environments designed for continuous collaboration with internal and external stakeholders.
They replace the fragmented sharing of sensitive information via email, isolated cloud folders, or disconnected tools with one or more persistently governed data spaces. Within these spaces, collaboration, approvals, and usage are managed in a granular, traceable, and controlled manner.
The core principles are:
-
data sovereignty remains with the data owner
-
usage and access rights are shared selectively and under control
-
collaboration is structured and dynamic across project and organizational boundaries
Connected Data Spaces are not intended for one-off data transfers. They are designed as a persistent environment for ongoing, trusted collaboration, especially in complex multi-stakeholder and multi-vendor projects.
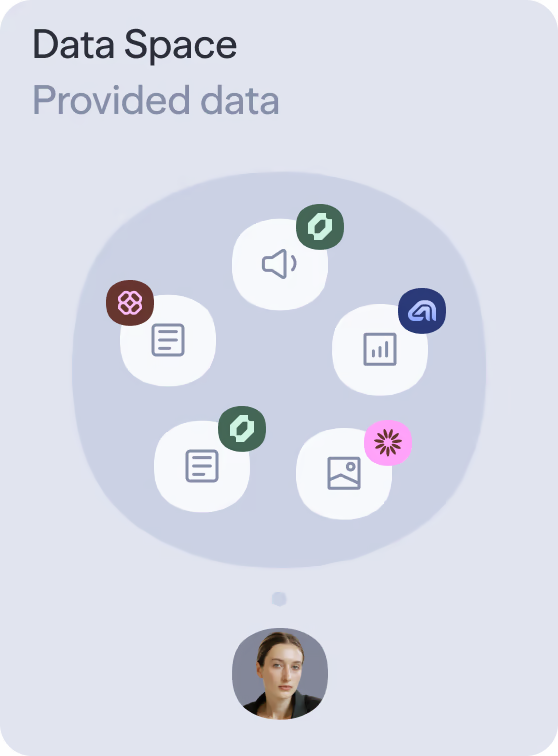
How do organizations retain control over data sovereignty, access, and approvals?
Within Connected Data Spaces, data sovereignty always remains with the data owner.
Access and usage rights can be shared with other parties in a targeted, controlled, and adjustable manner at any time.
In practice, this means:
- access rights are assigned granularly and based on roles
- approvals can be controlled by time, content, and context
- permissions can be expanded, restricted, or revoked without relinquishing control over the data
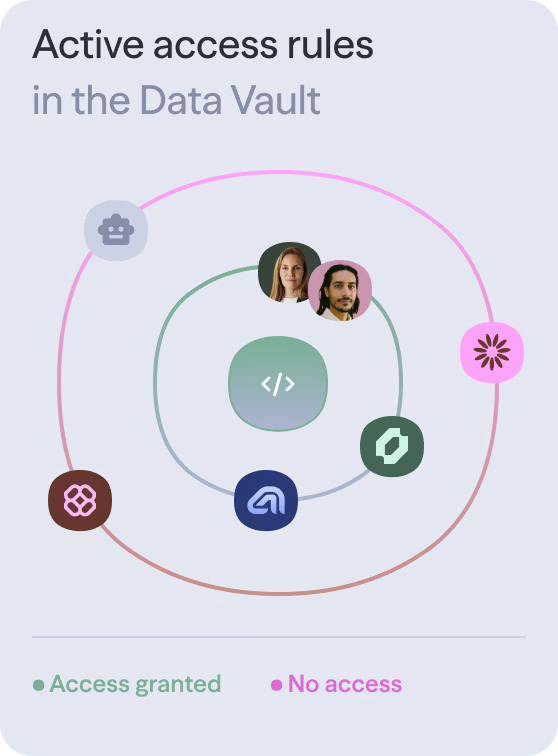
A distinctive feature is the visual representation of access and approval structures.
on:mint clearly shows:
- who has access to which data
- which approvals are active or have existed in the past
- how individual data spaces are connected
This ensures transparency and active control even when many parties are involved.
How do Connected Data Spaces support collaboration in complex projects?
Connected Data Spaces are built specifically for collaboration.
Organizations can:
- operate multiple data spaces in parallel
- assign them to different customers, partners, or suppliers
- selectively and securely connect individual data spaces
This makes it possible to manage complex multi-vendor projects involving multiple external parties at the same time, without unintentionally mixing or exposing sensitive information.
Depending on the project structure, data spaces can be organized and connected in parallel, hierarchical, or network-based configurations.
The data owner retains full control over structure, content, and approvals at all times.
How are originals, data integrity, and protection against manipulation ensured?
on:mint Connected Data Spaces ensure that the original digital asset is always shared, not copies or modified versions.
This is achieved through:
- content-based addressing, where each file is uniquely identifiable via its cryptographic fingerprint
- gated IPFS for private, access-restricted, and redundant storage
- blockchain-based attestation of relevant transactions and states
Manipulation or undetected changes are technically prevented.
As a result, Connected Data Spaces are suitable for use cases in which data integrity and authenticity are business-critical.
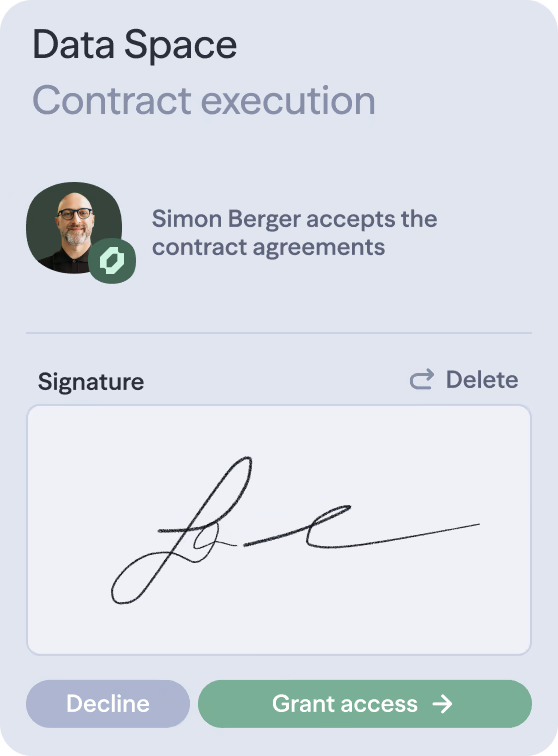
Can documents and contracts be signed in a legally binding way within Connected Data Spaces?
Yes. Documents can be electronically and cryptographically signed within Connected Data Spaces.
The signature ensures that:
- the document content is clearly defined
- the signer can be technically attributed
- the time and immutability of the signature are provable
The signature is integrated directly into the data space and becomes part of the documented collaboration.
This enables contracts, approvals, and agreements to be concluded without media breaks.
Compliance with eIDAS is currently undergoing final review.
Can Connected Data Spaces be customized to match a customer’s corporate identity?
Yes. Connected Data Spaces can be adapted to the customer’s corporate identity.
This includes:
- logo and color scheme
- visual design of the interface
- customer-specific naming and structures
A branded data space strengthens trust, professionalism, and orientation, particularly when working with external parties.
Depending on scope and effort, individual branding customizations may incur additional costs. These are defined transparently on a project-by-project basis.